Transport-based enforcement system is on. Emails from persistently vulnerable systems are being blocked as you read this.

Microsoft throttles and even blocks emails sent from Exchange Server to Exchange Online. The transport-based enforcement system reports emails sent from vulnerable Exchange Servers. The system initially introduces delivery delays that gradually increase, eventually blocking mail flow completely to force admins to update their on-prem environments. This is to ensure superior security of Microsoft 365 organizations. See if the feature affects you and what you can do to keep your mail flow running.
Who is affected by the new Exchange throttling policy?
According to this Exchange Team article, the update is aimed to combat “persistently vulnerable Exchange Servers”.
The system will be rolled out in stages. At first, the transport-based enforcement system will only apply to Exchange Servers that connect to Exchange Online using an inbound OnPremises connector. In other words, only hybrid environments will be affected at first. However, according to Microsoft, the system’s primary objective is to prevent potentially malicious emails from entering Exchange Online and to force organizations to patch their on-premises servers. So it’s safe to expect that eventually it will also affect organizations that fail to secure their on-prem environments, even when they’re not in hybrid.
Transport-based enforcement system applies only to high-risk environments, that is, “persistently vulnerable Exchange Servers”. Let’s see what it means.
What is a persistently vulnerable Exchange Server?
A persistently vulnerable Exchange Server is an Exchange Server instance for which there are known vulnerabilities that have not been addressed yet. So, if there is a security update (SU) you’ve been saving for later, know that the clock is ticking.
The bigger problem is when you’re on an Exchange Server version that has reached its end of life (or “end of Extended Support,” if you prefer official names). This means that your version will not receive any further SUs. In other words, it’s in the transport-based enforcement system’s crosshairs already.
How to check if my tenant is affected?
The Exchange admin center (EAC) features reports dedicated to this specific scenario. Go to the Exchange admin center > Reports > Mail flow > Out-of-date connecting on-premises Exchange servers or use this direct link.
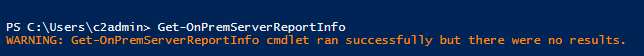
You can also connect to your Exchange Online organization using Connect-ExchangeOnline and then run
Get-OnPremServerReportInfo
If you get the following message, there’s nothing you need to do at the moment.
Email throttling & blocking timeline
There are two timelines that apply to Exchange Server’s mail flow throttling and blocking:
- Transport-based enforcement system’s stages. In other words, how the system handles reporting, throttling, and blocking.
- Feature rollout. Since email throttling and blocking can potentially affect (and harm) multiple organizations, Microsoft started with the oldest on-premises environments that supported hybrid and gradually added newer (less vulnerable) servers. Right now, we’re at the point where the transport-based enforcement system has been rolled out for all Exchange Server versions, including Exchange 2019.
Transport-based enforcement system stages
There are 8 stages in total. Stage 1 begins as soon as the system detects a non-compliant server. If the vulnerability is not resolved, the system will progress to the next stage after a specified period of time.
The first stage lasts 30 days, each next stage lasts 10 days.
- For the first 30 days, non-compliant server(s) will appear in the new mail flow report. During this period, there is no email throttling or blocking. It’s a warning phase that gives time to install the newest SU.
- Mail flow throttling begins. For 5 minutes every hour, emails will bounce with an SMTP 450 error. As a result, email delivery will be delayed.
- Throttle increases to 10 minutes per hour.
- The throttling period increases to 20 minutes per hour.
- Throttling caps at 30 minutes per hour. Email blocking begins. From this moment, for 5 minutes every hour, Exchange Online will bounce emails with a permanent SMTP 550 error. Those emails will not reach final recipients, and senders will need to send them again.
- The blocking period increases to 10 minutes per hour.
- The blocking period increases to 20 minutes per hour.
- The final stage, enforced after 90 days of non-compliance – this is when all emails from vulnerable server(s) will be blocked.
Rollout stages
The transport-based enforcement system has been introduced gradually. The start date marks the first instance when a specific Exchange distribution (version) was scanned for vulnerabilities, allowing Stage 1 Enforcement to begin.
As I said, the transport-based enforcement system is already live for all Exchange Server versions (except for Exchange Server Subscription Edition). Here’s how the rollout was staged:
- August 9, 2023 – Exchange 2007
- September 23, 2023 – Exchange 2010
- December 22, 2023 – Exchange 2013
- March 21, 2024 – Exchange 2016 and 2019
Exchange Team revealed plans related to the Transport Enforcement System
Ways to stay compliant
To prevent mail flow throttling and blocking don’t be behind with security updates of your Exchange Server. And, above all, make sure you don’t have any unpatched Exchange 2007 lurking somewhere in the basement.
If you have some legacy third-party solution that depends on an old Exchange 2010, it might be a good time to look for alternatives.
A short-term solution is to pause enforcement. You can request this option directly from the EAC mail flow report and you can use this option for up to 90 days per year to temporarily stop mail flow throttling and blocking if you let the system get beyond the Stage 1 (see enforcement stages). It’s an option that will be probably used a lot. Many companies follow a policy to wait before deploying SU on production environment to prevent rollbacks in case something breaks after an update. Which still does happen.
The 90-day limit is reset on the first day of the year.
Unfortunately, you won’t be able to ensure your on-premises environment’s security if you have an Exchange version that has reached its end of life. In this case, the only real way to move forward is to migrate to a supported Exchange version or to a cloud-only environment.
How to pause throttling and blocking by transport-enabled enforcement system
There are two ways to pause throttling and blocking of affected Exchange servers. Using either of them, you can ensure that your Microsoft 365 receives emails, even when your connected on-premises servers are not on schedule when it comes to updates.
In the Exchange admin center
Go to Exchange admin center > Reports > Mail flow > Out-of-date connecting on-premises Exchange servers > Enforcement Pause. You will see this option only if you have servers that were identified by the transport-enabled enforcement system as persistently vulnerable.
Using PowerShell
- First, connect to your Exchange Online organization using
Connect-ExchangeOnline. - Then, use the cmdlet below to check if there is an active enforcement pause:
Get-TenantExemptionInfo -BlockingScenario UnpatchedOnPremServer
Side note: The documentation on the cmdlet is limited at the moment. Please note that there are two additional blocking scenarios that you can check using this cmdlet. To get results for other scenarios, change the “-BlockingScenario” attribute value to: TenantRelayMessageRate or TenantOnPremRate. - Next, run the following cmdlet to create a pause (effective immediately) or to extend the pause that’s already in place:
New-TenantExemptionInfo -BlockingScenario UnpatchedOnPremServer -Number of Days /* Value up to 90 */
Interestingly, there is currently no cmdlet that would allow you to cancel the enforcement pause after you’ve updated the affected servers.
How do I migrate?
Migration under the pressure of time poses a lot of risks. Quite ironic, since in this scenario, migration is forced by a feature that should counter risks.
To migrate with confidence, use a dedicated migration tool. This way, you can benefit from:
- 24/5 technical assistance from people who handle complex migration projects on a daily basis.
- Streamlined and simplified migration process (no scripting or complex planning).
- Advanced reporting.
- Unlimited delta migrations to make sure each mailbox item is migrated.


